Cryptanalysis

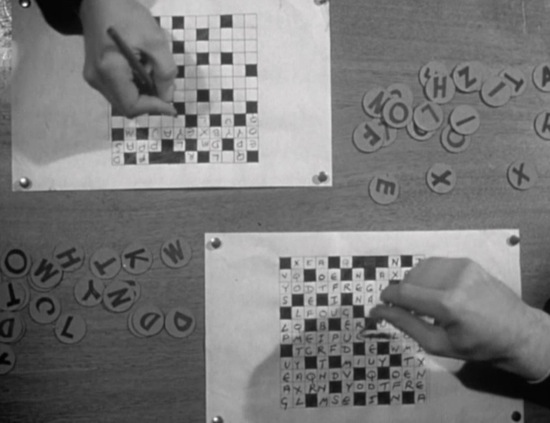
In the 1951 British drama Cloudburst (d. Francis Searle), Robert Preston — standing, at left, in the scene shown below — is a wartime cryptographer for the Special Operations Executive, a clandestine organization known as “The Ministry of Ungentlemanly Warfare.” He and his (mixed-gender) team labor night and day, using various scientific-looking methods, until they’ve successfully cracked the enemy’s code.

Because commercial semiotics has borrowed from Barthes and structural anthropology the notion of “cultural codes” (symbols and systems of meaning that are relevant to members of a particular culture), practitioners in the field have implicitly or explicitly claimed that they are in the business of cracking codes, and providing clients with a key which will unlock these codes. Here, then is the first of several notes on the discipline of cryptanalysis, in search of resonances and dissonances with the discipline of applied semiotics.

Here’s one of many possible approaches to making such a comparison of disciplines…
Following the structuralists, many commercial semioticians implicitly express the belief that cultural is a system of signs, and that as such, it has a structure — which is the “real thing” undergirding a surface reality, whose meanings are merely apparent meanings. The position of each element within that structure is determined by the whole. Commercial semioticians are plutonian spelunkers, uniquely able to get beneath a culture’s surface reality and map its underlying structure. Returning to the surface with this map, they can then unlock the culture’s codes. Poststructuralists might take into account the notion that human agency can alter these structures — but we still buy into the structures’ reality, thus failing to insulate ourselves from criticisms like anthropologist Adam Kuper’s: “Structuralism came to have something of the momentum of a millennial movement and some of its adherents felt that they formed a secret society of the seeing in a world of the blind.”
Are cryptanalysts a secret society of the seeing in a world of the blind? During World War II — if Cloudburst, which was based on real-life cryptographer Leo Marks’ experiences, is a reliable indication — that’s exactly how they viewed themselves. Marks seems to have believed that this was a form of hubris, and that anyone who viewed himself that way was riding for a fall. In Cloudburst, when Robert Preston’s character’s wife is killed in a hit-and-run automobile accident, he turns his considerable analytical abilities to the problem of identifying and murdering the culprits. “He had murdered once!” declaims the movie’s poster. “Now he was ready to strike again… and no one could catch him but himself!” It’s interesting to note that Marks also wrote the story on which the cult classic 1968 drama Sebastian — about a cryptographer for British Intelligence (Dirk Bogarde) whose self-regard for his own analytic ability leads him to fall into the hands of foreign agents — is based. Perhaps there is a moral here for hubristic commercial semioticians; traditionally, the antidote to hubris is a humble recognition of one’s limits.
Two other avenues to explore, off the top of my head:
- Cryptanalysis, like commercial semiotics, targets weaknesses in the cryptography — it looks for ways beneath the surface reality (a jumble of apparently meaningless signs) and seeks the underlying structure which allows us to make sense of those signs. But black-ops types will tell you that there are more efficient methods of finding out what a coded message says: bribery, physical coercion, burglary, spying, and trickery, to name a few. Can commercial semioticians find inspiration from these methods to crack cultural codes? I’m being provocative — but maybe this sort of thing is already going on. For example, when anthropologists hired by ad agencies are embedded in a typical target consumer’s home, where they observe the consumer’s interactions with cereal boxes and so forth… isn’t this an effort to beat commercial semioticians to the punch? By spying, that is to say, instead of desk-based code cracking?
- In the mid-1970s, the field of cryptanalysis adopted symmetric key cryptography, which underpins such Internet standards as TLS, PGP, and GPG encryption. Asymmetric key cryptography encodes and decodes messages via mathematical relationships (I don’t pretend to understand them) which have no efficient solution. The key used to encrypt a message is not the same as the key used to decrypt it. A common analogy is a locked mailbox with a mail slot: anyone can drop a message through the slot, but only the person who possesses the key can open the mailbox and read the messages. Commercial semioticians who attempt to think-with asymmetric key cryptography won’t be any less tempted to regard themselves as members of a secret society of the seeing… but perhaps they’ll be less likely to regard non-semioticians as “blind.” If the encryption key is open-source, then anyone — everyone — is potentially a coder.
This post is not intended to make a case of any kind; it’s a conversation starter.